How to Stay Safe From Hackers
In an era where digital technology is deeply interwoven into our daily lives, the threat posed by hackers has never been more prominent. From phishing scams to sophisticated AI-powered attacks, the arsenal of tools at a hacker's disposal is vast and continuously evolving. Understanding these threats is the first step in safeguarding our digital footprint. In this blog, we will delve into the myriad ways hackers can infiltrate your digital space and, more importantly, how you can bolster your defences against these intrusions. Staying safe in the digital realm requires vigilance, awareness, and a proactive approach to cybersecurity. Let's embark on this journey of digital self-defence.
The Rubber Ducky – USB

The Rubber Ducky is indistinguishable to other USB drives. It can deliver harmful payloads of data onto your PC, Mac, or even smartphone in seconds. It does this by appearing to your computer as a HID (Human interface device) such as a keyboard or mouse.
What Does This Mean?
The Rubber Ducky can bypass nearly all consumer grade anti-virus software’s, once bypassed it can do practically anything, it can delete and send files, it can create a backdoor to your computer for the hacker, it can do anything the hackers think of to your computer.
The primary function of the Rubber Ducky is to automatically execute a pre-programmed set of keystrokes at a very high speed. These keystrokes can perform a variety of tasks, such as opening a command line, downloading and executing malicious software, or extracting sensitive data. The actions are limited only by what can be achieved through keyboard inputs and the creativity of the attacker.
Hackers can program the Rubber Ducky using its own scripting language. Scripts are written on a computer and then loaded onto the device. When the device is plugged into a target computer, it executes these scripts.
Although the Rubber Ducky can be used for nefarious tasks like hacking, it was originally designed to help people do repetitive tasks faster and easier. For example, loading multiple programs and software on to hundreds of computers. It can also be used as a valuable tool for cybersecurity professionals. It can be employed to test an organisation's defences against USB-based attacks and raise awareness about the importance of physical security.
How to Protect Yourself Against The Rubber Ducky
Never plug a USB drive that you found on the floor into a computer. Not even to try find the owner of said USB device.
Always buy a USB device from reputable sources.
The O.MG Charging Cable
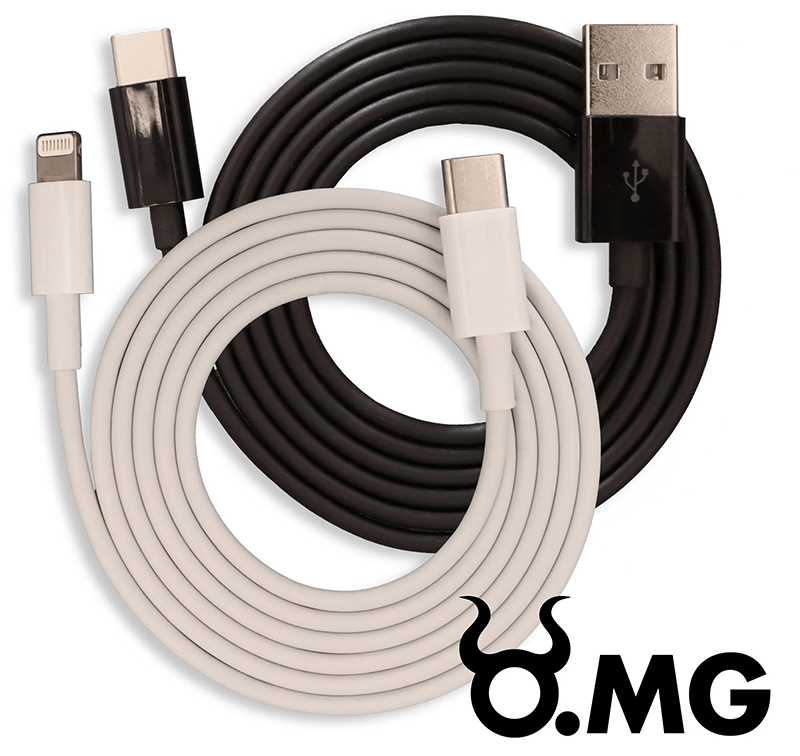
The O.MG Cable is a sophisticated hacking tool disguised as an ordinary charging cable (such as a USB or Lightning cable). This device has gained attention in the cybersecurity community for its ability to facilitate remote attacks.
This cable is indistinguishable from other charging cables. To your computer or smartphone, it disguises itself as a human interface device. It can be programmed to disguise as a branded mouse or keyboard making it almost undetectable to nearly all anti-virus software.
The cable contains a tiny wireless implant, enabling it to connect to a Wi-Fi network. This feature allows a hacker to remotely communicate with the cable from a short distance, typically a few hundred feet.
The hacker can remotely connect to the O.MG Cable via Wi-Fi to execute commands, access data, or manipulate the connected device. This remote capability significantly increases the potential impact of the cable, as the attacker does not need to be physically present to control the device.
Similar to the Rubber Ducky, the O.MG Cable can also be a valuable tool for security professionals. It can be used to test an organisation's vulnerability to physical device attacks and to train personnel to be cautious about using unknown cables.
How to Protect Yourself Against The O.MG Cable
Never use public charging stations and if you do, use a data blocker. This allows power to pass through, but not data. Here is an example of a data blocker.
Always buy charging cables from reputable sources
Never use a charging cable you have found.
Flipper Zero

Flipper Zero is a multi-functional tool designed for cybersecurity enthusiasts, hardware hackers, and IT professionals. Its versatility and user-friendly design have made it popular for a variety of hacking-related activities.
The flipper Zero can monitor and replicate signals, such as Bluetooth, NFC such as wireless transactions, infrared, GHz such as garage doors and keyless systems.
What does this mean?
The Flipper Zero can read and emulate RFID and NFC tags like access control systems, such as those used in buildings or public transport systems.
It can capture, analyse, and replay radio signals. Meaning it can interact with garage door openers, car key fobs, wireless alarm systems, and many more.
The Flipper can monitor Bluetooth devices such as wireless keyboard and mice. Making it a great wireless keylogger for hackers.
Flipper Zero's hacking potential is largely centred around its ability to analyse, mimic, or interact with a variety of electronic and wireless systems.
How to protect yourself against Flipper Zero
Use signal blocking technology for anything that is RFID and NFC.
Do not use Bluetooth peripherals in public places.
Use radio devices when no one is around, like opening your garage door.
Phishing
Phishing involves sending fraudulent emails or messages that resemble those from reputable sources to trick individuals into revealing personal information, like passwords and credit card numbers.
Many phishing attacks target bank accounts through online banking. They will set up a false website that looks almost identical to your online banking. Then send you an E-mail with a link to said website. From there the hackers will log your email address and password. They may also ask for your mobile number.
Another more recent form of phishing is that hackers will spoof a colleague’s email address, normally a person of high authority in the organisation. Then email you to buy perform a task, usually involving financial obligations.
How to Protect Yourself Against Phishing
Never click on links or download attachments from unknown or suspicious emails. If you are unsure, ring the company you have been sent the email from.
Hover over the name of the sender to reveal their email address. If you do not recognise the address, report the email and delete it.
Malware
Malware stand for Malicious Software, it can be used to damage or disable computers, steal data, or gain unauthorised access to networks. There are many different types of malware:
- Viruses: Attach themselves to clean files and infect other clean files. They can spread uncontrollably, damaging a system's core functionality and deleting or corrupting files.
- Worms: Reside in the memory of infected computers and replicate themselves across networks, exploiting vulnerabilities in operating systems.
- Trojans: Disguise themselves as legitimate software or are hidden in legitimate software that has been tampered with. They tend to act discreetly and create backdoors in your security to let other malware in.
- Ransomware: Locks down a victim’s files or computer and demands payment in order to regain access.
- Spyware: Secretly records what a user does, so that cybercriminals can make use of this information. For example, it could capture credit card details.
- Adware: Delivers unwanted ads or redirects search requests to advertising websites. While not always malicious in intent, aggressive advertising software can undermine security just to serve ads.
- Botnets: Networks of infected computers that are made to work together under the control of an attacker.
How to Protect Yourself Against Malware
Use antivirus software, and make sure its up to date to prevent the latest versions of these attacks.
Regularly update your devices software, keeping your operating systems and software up to date can patch security holes that malware could exploit.
Avoid visiting untrustworthy websites and download software only from reliable sources.
Be cautious about opening email attachments or clicking on links in email messages, especially if they come from unknown sources.
Man-in-the-Middle (MitM) Attacks
A man in the middle attack is where an attacker secretly intercepts and possibly alters the communication between two parties who believe they are directly communicating with each other.
For example they can eavesdrop on a network, capturing sensitive information like login credentials, credit card numbers, and personal data.
MitM attacks are particularly dangerous because they can be hard to detect, and the attacker can capture a large amount of sensitive data without being noticed.
How to Protect Yourself Against Man in the Middle Attacks
Avoid using public Wi-Fi for sensitive transactions. If necessary, use a VPN to encrypt your data.
Implement 2FA (two factor authentication) to add an extra layer of security for user accounts, reducing the risk if credentials are intercepted.
Social Engineering
Social engineering is a method of manipulation that exploits human psychology, rather than technical hacking techniques, to gain access to information, systems, or networks. It is essentially the art of tricking people into revealing confidential information or performing actions that may compromise the security of an individual or an organisation. Here are some key aspects:
- Phishing: This is one of the most common forms, where attackers send fraudulent emails or messages that appear to be from reputable sources to trick people into revealing sensitive information, such as passwords and credit card numbers.
- Spear Phishing: A more targeted form of phishing, where the attacker customises their approach for a specific individual or organisation, making the fraudulent communication seem more legitimate.
- Pretexting: The attacker creates a fabricated scenario to persuade a victim to divulge information. This often involves an attacker pretending to need information to confirm the identity of the recipient.
- Baiting: Similar to phishing, baiting involves offering something enticing to the victim in exchange for private information. This could be in the form of a physical (like a USB drive labelled “Confidential”) or a digital lure (like a download of some sort).
- Tailgating or Piggybacking: Here, unauthorised persons physically follow authorised persons into a restricted area or system, often under the guise of being a fellow employee.
- Quid Pro Quo: Offers a benefit in exchange for information. This could be something like a hacker posing as a technical support agent offering to fix an issue in exchange for the victim installing malware.
How to Protect Against Social Engineering Attacks
Regular training and awareness programs can help individuals recognise and avoid social engineering attempts.
Implementing strict policies and procedures for verifying identities and handling sensitive information can reduce the risk.
Always verify the legitimacy of a request for sensitive information, especially if it's unusual or unexpected.
Be cautious about how much personal information you share online. Social media platforms can be a goldmine for attackers.
Implementing physical security measures like access cards, badges, and security personnel can help prevent tailgating.
AI Powered Attacks
AI-powered attacks represent a sophisticated and rapidly evolving threat in the realm of cybersecurity. These attacks utilise artificial intelligence and machine learning to enhance traditional hacking techniques, automate attacks, or create new methods of exploitation. Here are some types of AI powered attacks:
- Phishing Attacks: AI can be used to craft convincing phishing emails by analysing large datasets of legitimate emails and creating messages that are highly personalised and more likely to deceive the recipient.
- Password Attacks: AI algorithms can rapidly generate and test password combinations, making brute force attacks more efficient.
- Malware Development: AI can help in creating more sophisticated malware that can adapt, learn from the environment, and evade detection.
- Social Engineering Attacks: AI can analyse personal data from various sources to automate and personalise social engineering attacks, making them more effective.
- Exploiting AI Systems: Attackers might also target AI systems themselves, using techniques like data poisoning (feeding misleading data into the system) or exploiting biases in AI algorithms.
How to Protect Against AI Powered Attacks
Just as AI can be used for attacks, it can also be used for defence, such as in the development of AI-based threat detection systems that can identify and react to threats in real-time.
Organisations must continuously monitor their networks and systems for unusual activities and adapt their security measures accordingly.
Safeguarding the data used to train AI systems is crucial to prevent data poisoning attacks.
Keeping up with the latest developments in AI-powered attacks and educating security professionals about these threats is essential.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
These attacks overwhelm a system's resources, rendering it unable to respond to service requests, often by flooding it with superfluous requests. These attacks can be devastating, causing extended downtime and significant economic damage.
Denial-of-Service (DoS) Attacks
A DoS attack originates from a single internet connection, aiming to overwhelm a targeted server or network with traffic. This can cause the server to slow down or crash, denying service to legitimate users.
Common techniques include flooding the target with superfluous requests, exploiting a vulnerability to cause the system to crash, or sending malformed or oversized packets.
Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks are an extension of DoS attacks but are executed from a distributed network of connected devices, often a botnet. This makes them more challenging to mitigate as they generate traffic from multiple sources.
Hackers use a large number of hijacked computers or IoT devices to launch a coordinated attack. These devices may be spread across the globe, and their owners are typically unaware that their devices are being used maliciously.
Types of DoS and DDoS Attacks
- Volume-Based Attacks: The goal is to saturate the bandwidth of the targeted site. Examples include UDP floods and ICMP (Ping) floods.
- Protocol Attacks: These attacks target server resources or intermediate communication equipment, like firewalls and load balancers. SYN floods and Ping of Death are examples.
- Application Layer Attacks: These target web applications and are designed to be as disruptive as possible by exhausting a resource in the application layer. HTTP flood is a common type.
How to Protect Yourself Against DoS and DDoS Attacks
Having more bandwidth than you typically need can help absorb the volume of an attack.
Implement DDoS protection services and solutions that can detect and mitigate incoming attacks.
Design your network to handle unexpected traffic surges and to segregate traffic types.
Have a detailed response plan in place to quickly and effectively respond to attacks.
Regular audits can help identify potential vulnerabilities and prepare for possible attack scenarios.
Brute Force Attacks
Brute force attacks are a method of trial and error used to gain access to information such as a user password or personal identification number (PIN). In these attacks, an attacker tries many passwords or phrases with the hope of eventually guessing correctly. The attacker systematically checks all possible passwords and passphrases until the correct one is found.
How to Protect Yourself Against Brute Force Attacks
Use long, complex passwords that combine letters, numbers, and symbols. The more complex the password, the harder it is to crack.
Implement account lockout policies after a certain number of failed logins attempts to prevent automated attempts.
Use MFA, which requires additional verification beyond just a password, significantly increasing security.
Encourage the use of password managers that can generate and store complex passwords.
Although not always practical, regular password changes can help mitigate the risk of brute force attacks.
Use CAPTCHA tests on login pages to prevent automated scripts from executing brute force attacks.
Final Notes on How to Stay Safe from Hackers
In conclusion, our exploration of various hacking methods, from the sophistication of AI-powered attacks to the blunt persistence of brute force attacks, underscores the evolving landscape of cybersecurity threats. Mitigating these risks requires a multifaceted approach, including robust security protocols, continuous education, and awareness.
As technology advances, so do the techniques of attackers, making it imperative for individuals and organisations to stay vigilant and proactive. By understanding the nature of these threats and implementing effective defence strategies, we can better safeguard our information and digital assets in this ever-changing digital world.


